項目地址:https://github.com/ThomasTJdev/WMD
大規模殺傷性武器(Weapon of Mass Destruction)
這是一款用 Python 寫的安全工具集。軟件封裝于“模塊”中。模塊主要由純 Python 代碼和第三方程序組成。
主要功能
1) 要使用模塊,運行命令 "use [module_call]",例如使用 "use apsniff" 激活模塊。 2) 可以使用 "set [parameter] [value]" 更改模塊選項。 3) 在模塊內,可以用命令 "so" 查看選項。 4) 環境設置位于 core/config.ini 中。請在運行程序之前進行調整。
截屏:

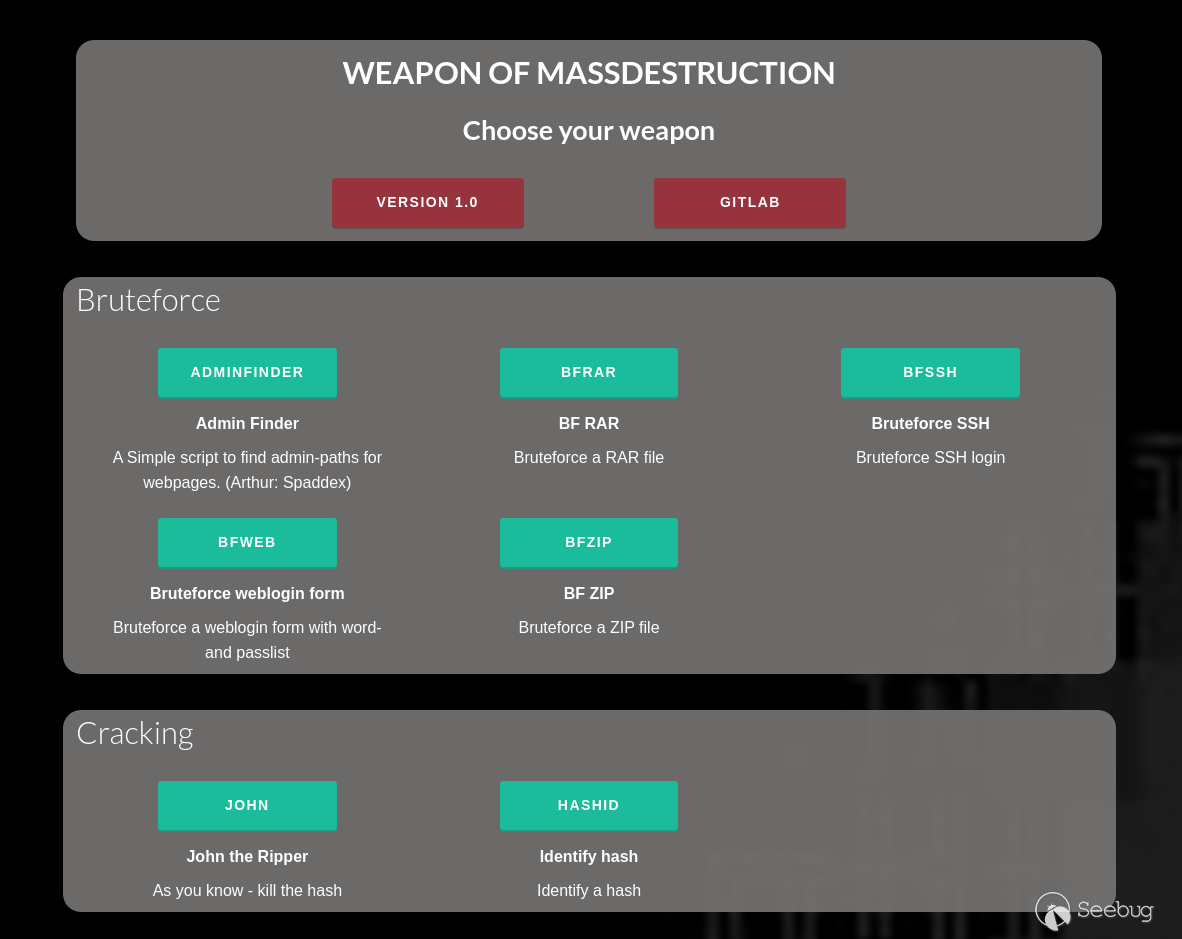
Web 界面
控制臺運行命令“www”,激活 Flask 服務,即可在瀏覽器中展示模塊。通過 127.0.0.1:5000 訪問。
模塊會直接加載到 xterm 中。
DEV: 可以試一下 SniffHTTP 和 APsniff 模塊 - 可在瀏覽器中定義參數。
Screenshot:
模塊列表
| CAT: | TYPE: | CALL: | NAME: | DESCRIPTION: |
|---|---|---|---|---|
| bruteforce | creds | changeme | Default creds scan | Scan IP's for services and try logging in with default credentials (Arthur: ztgrace) |
| bruteforce | loginpath | adminfinder | Admin Finder | A Simple script to find admin-paths for webpages. (Arthur: Spaddex) |
| bruteforce | rar | bfrar | BF RAR | Bruteforce a RAR file |
| bruteforce | ssh | bfssh | Bruteforce SSH | Bruteforce SSH login |
| bruteforce | web | bfweb | Bruteforce weblogin form | Bruteforce a weblogin form with word- and passlist |
| bruteforce | zip | bfzip | BF ZIP | Bruteforce a ZIP file |
| cracking | aut | john | John the Ripper | As you know - kill the hash |
| cracking | hash | hashid | Identify hash | Identify a hash |
| cracking | wpa | crackwpa | Crack WPA 4-way handshake | Gather WPA 4-way handshake from accesspoint and crack it |
| exploit | browser | browserpwn | Browser Autopwn2 | This module will automatically serve browser exploits (Arthur: sinn3r[at]metasploit.com) |
| exploit | search | exploitdb | Exploitdb | Shell-style script to search exploit-db.com exploits. (Arthur: mattoufoutu) |
| sin | mspoofcheck | Spoofcheck email domain | Check if a domain can be spoofed for e.g. emailing | |
| monitor | arp | arpmon | ARP monitor alert | Monitor ARP table and alert for changes |
| monitor | ip | ipmon | IP monitor alert | Monitor IP's and alert for changes |
| other | settings | settings | Change settings | Change your environment settings, e.g. interface |
| pentesting | niptt | sparta | SPARTA | SPARTA is a python GUI application which simplifies network infrastructure penetration testing. |
| phishing | ap | etphis | Ewil Twin phishing | Create a Evil Twin and redirect user to fake password page. |
| phishing | webpage | webphis | Webpage phishing | Run a local flask server with phishing pages. |
| recon | dns | dig | Domain info groper | Using dig command you can query DNS name servers for your DNS lookup related tasks |
| recon | dns | dnsmap | dnsmap | DNS Network Mapper. Enumeration and bruteforcing. |
| recon | dns | dnsrecon | dnsrecon | Multiple DNS recon abilities. |
| router | framework | rsploit | Routersploit | Framework for routers with exploits and getting creds. (Arthur: Reverse Shell Security) |
| scan | sin | lanscan | Lan scan | Scan local net - recon |
| sniff | aut | apsniff | AP sniff | Create AP and sniff HTTPS and avoid HSTS + Beef |
| sniff | http | sniffhttp | Sniff HTTP | Sniff HTTP packages. Extract username and passwords from traffic. |
| sniff | sin | bettercap | Bettercap | Bettercap integration for sniffing packets and bypass HSTS and HTTPS |
| socialeng | instabot | Instagram bot | Instagram bot for performing various activities (Arthur: LevPasha) | |
| spoof | arp | arpspoof | ARP spoof | Spoofing ARP |
| sql | sqli | gdsqli | Gdork SQLi | Scrape net for urls and check if they are prone to SQL injection |
| sql | sqli | sqlmap | SQLmap | Just an activation of SQLmap. |
| system | mac | macc | Macchanger | Change your MAC address |
| tools | search | searchht | Search hacktools | Searchengine for hackingtools |
| wifi | accesspoint | createap | Create an Accesspoint | Create an Accesspoint |
| wifi | wifi | wifiutils | WiFi utils | Utilities for WiFi, e.g. deauth, WiFi's, clients, probes, etc. |
運行
運行前:
1. 調整core/config.ini.default 中的環境選項。
2. 將 core/config.ini.default 重命名為 core/config.ini。
開啟終端:
python3 wmd.py
使用單獨的模塊:
python3 wmd.py -m [CALL]
開啟 web 服務:
python3 wmd.py -w
不檢查依賴運行:
python3 wmd.py -nc
環境要求:
- Linux 系統
- Python3
- Python 庫的要求位于 requirements.txt
可選項 tools/software/GIT:
這些模塊需要時會通知你,并不會直接運行
- GIT: Admin-Finder
- Aircrack-ng
- Airomon-ng
- Airodump-ng
- Airolib-ng
- Arp
- Arpspoof
- Beef
- Bettercap
- GIT: changeme
- CrackMapExec
- Create_ap
- Dig
- Dnsmap
- GIT: Dnsrecon
- GIT: Exploitdb
- GIT: Hashid
- Hostapd
- GIT: Instabot
- John the Ripper
- Nmap
- GIT: Routersploit
- SPARTA
- GIT: Spoofcheck
- GIT: XSSER
部署
項目結構
- core --> 核心文件中使用了所有的代碼。
- files --> 靜態文件,密碼列表等。
- logs --> 用于保存日志的標準文件夾。
- modules --> 包括各種模塊。
- tmp --> 你猜呢
- tools --> GIT 工具。
- www --> webserver 的文件。
新模塊
可以在 modules/module_template.py 中檢查模板。
添加模塊
Run python3 wmd.py -a modulePathName.py
 本文由 Seebug Paper 發布,如需轉載請注明來源。本文地址:http://www.jmbmsq.com/217/
本文由 Seebug Paper 發布,如需轉載請注明來源。本文地址:http://www.jmbmsq.com/217/